VMware Network Virtualization Solutions: A Deep Dive into NSX-Powered Software-Defined Networking
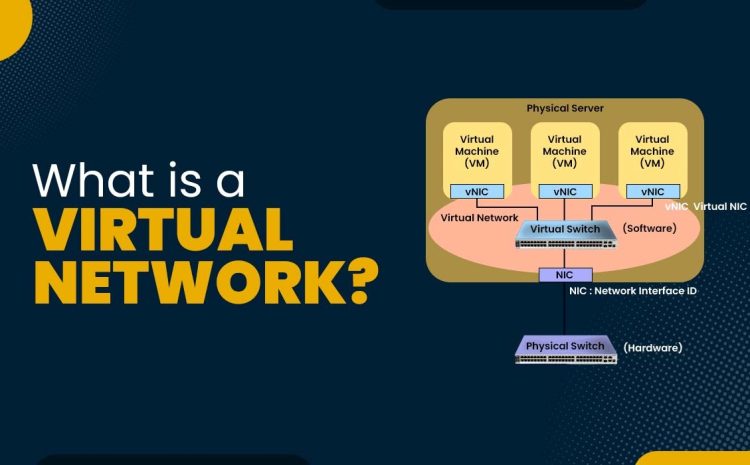
VMware is a leading company in virtualization and network management, offering a range of network virtualization solutions for organizations and network professionals. Each of these solutions provides excellent flexibility in network management and optimal resource…