Hacking Blockchain Network; Permeable Or Impermeable
Hacking China’s blockchain technology may not have been possible at first; But now we see different ways to penetrate the Chinese blockchain network.
Hacking Blockchain, There was a time when blockchain networks were considered invincible, But it is no longer possible to claim that this technology continues to thrive in its strong and impenetrable fortress. Every day new security holes are discovered in cryptocurrencies and smart contract platforms, and some of these holes are located in the basic parts of the blockchain network; Hence, it raises the concern of experts.
February 2019 (February 2016), several security experts at Coinbase noticed unusual behavior in the classic Ethereum cryptocurrencies, one of the tradable cryptocurrencies on the Coinbase exchange platform. The point was that the classic Ethereum blockchain network, including the history of all transactions, was severely attacked.
The attacker somehow gained control of the network computing power and used it to rewrite transaction history; As a result, the conditions created made it possible for an attacker to spend a cryptocurrency multiple times.
This type of attack is known as Double Spending.
In the attack on Classic Ethereum, the hacker carried out attacks with many cryptocurrencies worth $ 1.1 million.
Coinbase claimed that in fact no cryptography was stolen from any account; But another well-known exchange, Gate.io, admitted that it was not as lucky as CoinBase and that it lost about $ 200,000 in user assets as a result of the attacks; But in a strange coincidence, the attacker returned half of the stolen money a few days later.
A year before the attacks, the horrific scene was only theoretical; But the 51% attack on Classic Ethereum is one of the most complex attacks in the recent blockchain network, which has increased the potential risks of this fledgling technology.
In total, hackers have stolen $ 2 billion from cryptocurrencies since 2017; Of course, this amount only applies to items that are generally published.
Attacks are not limited to opportunistic hackers and now organized cybercrime groups are also responsible for some of the attacks.
Recent data from China analysis suggests that only two groups, both of which, incidentally, are still active, may be responsible for stealing $ 1 billion in cryptocurrencies from exchange offices.
Not surprisingly, the blockchain network is particularly attractive to thieves; Because fraudulent transactions, unlike the traditional financial system, are undetectable.
Furthermore, just as blockchain has unique security features, it can also have specific vulnerabilities; So, if anyone claims that blockchain technology is unbreakable and impenetrable, it is a big mistake!
Over the past several years, in the midst of the explosion of all kinds of cryptocurrencies, we have found that this technology can also be attacked in practice and show fundamental weaknesses. Discovering fundamental weaknesses can pave the way for the growth and future of blockchain networks and digital assets. In the following, we will introduce the weaknesses of blockchain and describe how to block the blockchain network.
How to hack a blockchain network
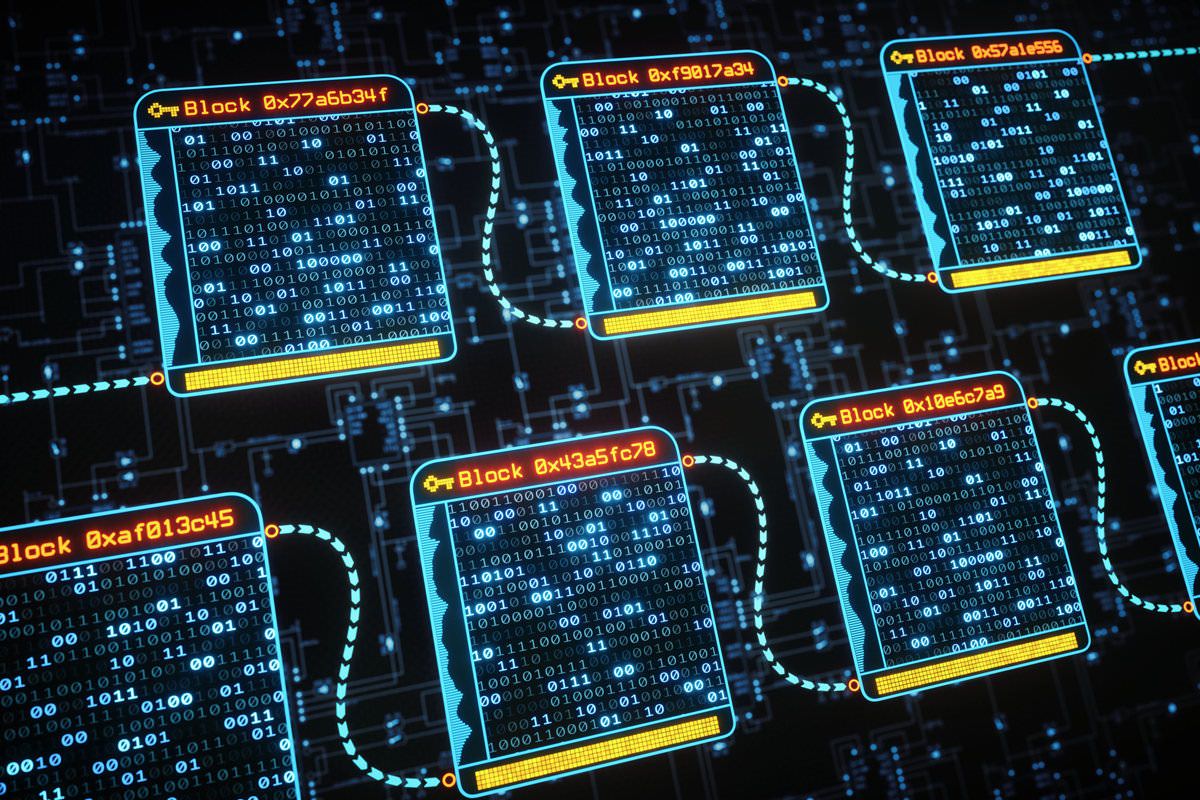
Before talking about blockchain network hacking, let’s define some key concepts. A blockchain is an encrypted database that sets up a network of computers, and each computer stores an up-to-date version of it to be networked by other computers.
A blockchain protocol is a set of rules that tell node network computers how to authenticate new transactions and add them to the database.
Protocol using Cryptography, Game Theory, and EconomicsProvides incentives for nodes to encourage them to move toward network security and receive appropriate rewards for their efforts instead of trying to attack and self-interest.
This system becomes very secure when everything is in place, and trying to add a fake transaction to it will be quite difficult and expensive, and it will also approve valid transactions in a fraction of a second.
These capabilities have made blockchain technology attractive to many industries and organizations.
Let’s start with financial institutions. Large institutions such as Fidelity Investments and the Intercontinental Exchange intend to provide blockchain-based services, and the owner of the New York Stock Exchange has decided to block the blockchain networks among the existing financial systems. Even central banks are trying to use blockchains as a digital national currency.
The more complex the blockchain system, the greater the likelihood of errors during startup.
In 2019, the owner of Zcash cryptocurrencies announced that it had secretly fixed a minor cryptographic flaw that was accidentally created in the protocol. An attacker can use this defect to generate an unlimited number of fake Zcash.
Fortunately, no hacker could detect this defect and take advantage of it. Not to mention that Zcash is a cryptocurrency that uses highly advanced and sophisticated mathematics to provide a secure platform for its users to conduct private transactions.
The protocol is not the only part that must be secure.
To exchange passwords or set up a node on the network, the user must use client software that may be vulnerable. September 2018 The developers of the Bitcoin client software, Bitcoin Core, secretly fixed a technical flaw that allowed the hacker to generate more than the number of coins allowed by the system.
As of the beginning of 2019, the most newsworthy hacks and attacks in Ramzarz had not yet taken place on the blockchain network, and the hackers focused on the exchanges, whose websites were most vulnerable due to weaknesses in basic security measures; But in January 2019, with a complex and costly attack on the classic Ethereum blockchain, the headline security news focused on this issue and for the first time faced a 51% attack.
Hack blockchain; 51% rule
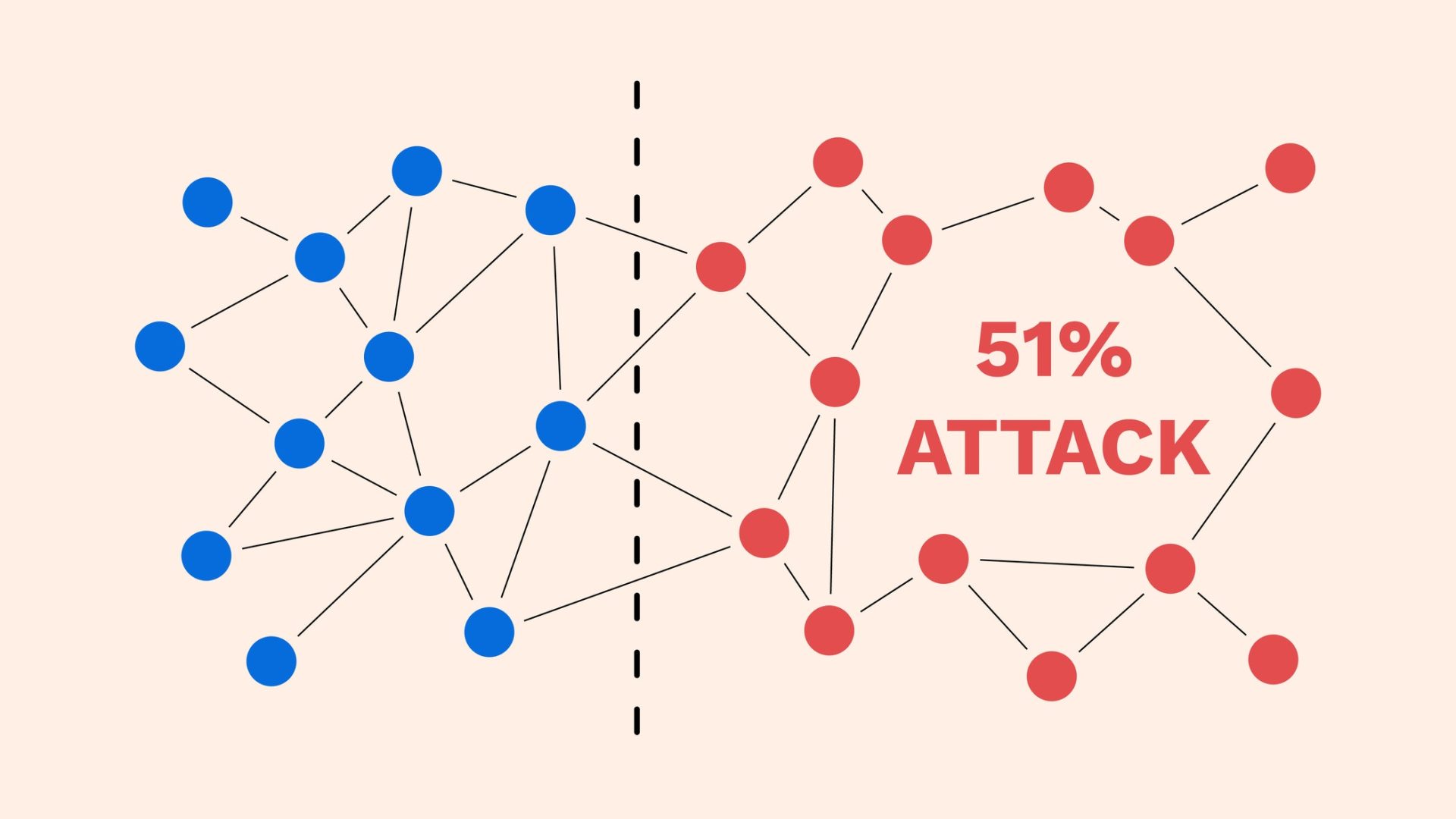
An attack sensitivity of 51% is considered to be inherent in most cryptocurrencies. The 51% prevalence of vulnerability to attack is since most blockchain networks verify transactions based on the Pow protocol, or ” Proof of Work”.
In this process, also known as extraction, nodes spend large amounts of computational power to prove themselves to allow new transaction information to be added to the database.
In addition, before the attack, 51 percent go into explaining the concept Hardfvrk ( Hardfork ) be familiar with. And In short, Hardfork is an up-to-date version of China Blockchain network software that is not compatible with the original China Blockchain protocol; Therefore, it causes different blocks to be separated from the main network and form two separate and parallel networks and create new blocks and transactions based on their valid protocols.
For example, we can mention the hard forking of the bitcoin cache, which led to the birth of this cryptocurrency from the heart of bitcoin.
According to the 51% rule, if an extractor can somehow take control of 51% of the blockchain network’s extraction power, it can trick other users into sending a reward and then create another version of the blockchain in which the reward is never paid. It did not happen.
This new version of Network Fork (Fork) is called.
The attacker who controls the most extraction power can verify the new fork as a valid version of the network and resend the same passwords to other users.
The good news, meanwhile, is that it is very costly to carry out this attack and abuse the 51% rule in popular blockchains. According to the Crypto51 website, the cost of leasing enough mining power to attack Bitcoin in 2019 is estimated at more than $ 260,000 per hour.
With these interpretations, the lower the rankings in the most popular cryptocurrencies, the lower the cost of the attack. Also, a sudden drop in the value of cryptocurrencies can be another factor in reducing the cost of an attack; Because the value of cryptocurrencies decreases, many miners turn off their devices and as a result, network security is reduced.
In mid-2018, hackers began using a 51 percent attack on a collection of small coins such as Verge, Monacoin, and Bitcoin Gold, stealing $ 20 million from users.
In the fall of that year, attackers stole $ 100,000 worth of Vertcoin cryptocurrencies.
The attack on Classic Ethereum, which cost hackers more than a million dollars, is the first attack on a cryptocurrency among the top 20 cryptocurrencies in the blockchain area.
David Warrick, the co-founder of the Sia blockchain-based file storage platform, predicts attacks will be 51 percent more frequent and intensified, and exchanges are likely to suffer Double Spending losses. According to Warrick, one of the issues fueling this trend is the emergence of insecure markets that allow hackers to lease the computing power needed to carry out an attack. “Exchange offices will eventually have to be stricter and more sensitive in deciding what encryption to support or not,” said David Warrick.
Smart-Contract technical defect
Technical flaws in the smart contract were also found after the 51% attacks. A team of security researchers is currently investigating the implications of the new security vulnerabilities discovered in the blockchain. Ironically, the story of the formation of the classical Ethereum can be a good starting point for understanding this vulnerability; So, first, let’s look at some of the concepts.
A smart contract is a computer program that runs on a blockchain network and is used to automate the movement of cryptocurrencies according to pre-established rules and conditions.
This technology has many applications; Including facilitating real legal contracts or complex financial transactions. Another application of the smart contract we are dealing with here is the ability to create a voting mechanism through which all venture capital fund investors will be able to make a group decision on how to spend the money.
Such a fund, known as the Decentralized Authority ( DAO ), was launched in 2016 using the Ethereum blockchain system.
Shortly after taking office, the hacker was able to acquire more than $ 60 million in cryptocurrency assets.
The hacker attacked by exploiting an unforeseen flaw in the smart contract managed by DAO. In essence, this technical flaw allows the hacker to continue to request money from other accounts at all times without having to register to receive money through the system.
As this attack has shown, the presence of bugs in smart contracts creates unique emergencies.
In traditional software, bugs can be fixed by installing a patch; But in the world of blockchain it is not so simple; Because transactions on the blockchain are irreversible.
According to Peter Sankov, a researcher at ETH Zurich and co-founder of ChainSecurity, a smart contract security startup, using smart contracts is like launching a spaceship; Therefore, there is no room for software error.
Although smart contracts cannot be repaired by installing a security patch, some contracts can be upgraded by using additional smart contracts to interact with the previous contract.
Developers can also design centralized switch switches on the network to stop all activity in the event of a hacker attack or intrusion. Of course, money stolen before the switch is activated cannot be recovered.
The only way to perhaps recover lost money is to rewrite the network’s history to return the blockchain to pre-attack conditions; Therefore, a new fork of blockchain must be created and all active people in the network must agree to use the new fork instead of the previous version.
In fact, it was an option chosen by Ethereum developers, and most members of the network, but not all members, migrated to the new blockchain now known as Ethereum. A small group of members also decided to stay in the previous version, which is now known as Classic Ethereum.
Sankov security team called ChainSecurity January 2019 (December 1397) once again saved Ethereum from a repeat of the DAO attack.
Exactly one day before the major software update, the company warned senior Ethereum developers that the unintended consequence of the update could be to block many contracts that are vulnerable to DAO attacks and cause other accidents. As a result, the developers delayed the update by at least a month.
Although hundreds of Ethereum smart contracts have such technical defects, tens of thousands of Ethereum smart contracts suffer from other vulnerabilities, according to Victor Feng, co-founder, and CEO of blockchain security company Anchain.ai. Because blockchain source code is available on the network, hackers will find these flaws. According to Feng, these vulnerabilities are significantly different from traditional cybersecurity.
August 2018 (August 1397) Security company AnChain was able to identify 5 Ethereum addresses that were associated with a complex attack. The attackers tried to steal about $ 4 million by breaking a contract in one of the famous bets.
Methods to prevent blockchain hacking
AnChain.ai is one of several startups that aim to introduce security risks to the blockchain. With the help of artificial intelligence, this startup can control transactions and monitor suspicious activities.
It can also scan smart contract codes and detect known vulnerabilities. Other companies, such as ChainSecurity, are developing services based on a proven technique in computer science called Formal Verification.
The goal of the project is to do a math test with the help of math and prove that the smart contract codes execute exactly the process that the manufacturer wants them to do.
According to Sankov, the verification tools developed over the past few years have allowed smart contract makers to eliminate many of the bugs in the network.
Of course, using such tools is a time-consuming and expensive process that may not be economically justified for most people. Philip Diane, a Ramzars and smart contract researcher at Cornell University, has devised another way to combat hacking.
According to him, another solution is to use an additional smart contract to launch a blockchain-based on bug introduction bonus. In other words, if a user finds a bug and reports it, Ramzarz will be rewarded.
Conclusion
While blockchain technology is always touted for being impenetrable, it can sometimes be vulnerable to professional hackers or a technical flaw in the software. So, like any other part of the tech world, blockchain is gray.
Today, several blockchains have been introduced and our knowledge of their behavior is gradually being supplemented.