What Is a Firewall and What Are Its Types
A firewall is a network Security device that allows home networks to exchange information securely.
The firewall prevents hackers from quickly infiltrating networks and eavesdropping on information.
Firewalls can be deployed across various architectures and configurations. They can be installed as software or hardware at sensitive points in computer networks and intercept any traffic entering or leaving the network.
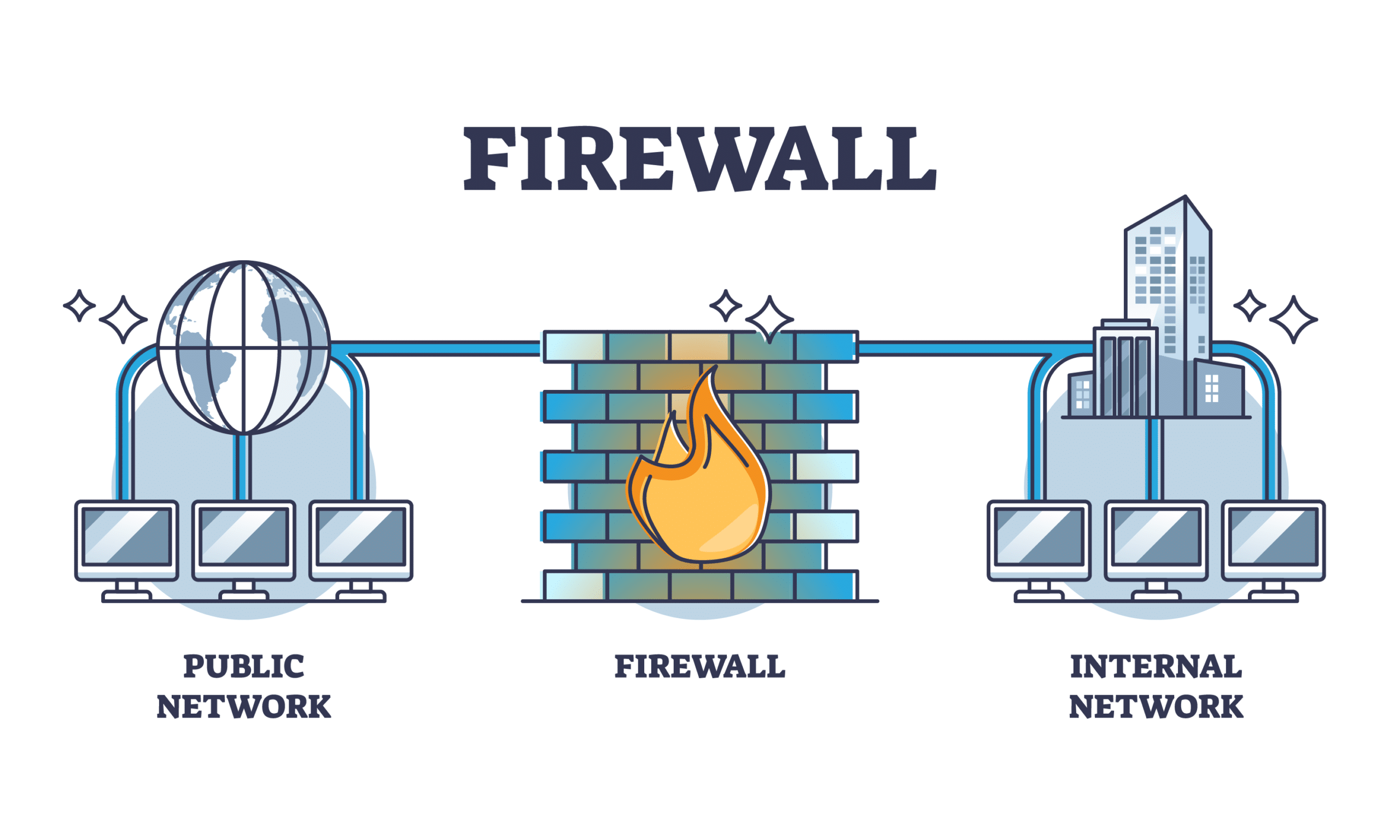
Firewalls are typically placed between an organization’s private and public networks, such as the Internet, to establish a secure connection.
Based on this definition, a firewall can be interpreted as a mechanism for information exchange between two networks.
How does a firewall work?
Now that you know what a firewall is and what it does, it’s time to figure out how it works. Firewalls inspect all packets that pass through their network interfaces to evaluate them and determine whether they should be permitted into the network, according to the rules and guidelines defined in the Access Control List (ACL) and by Security experts.
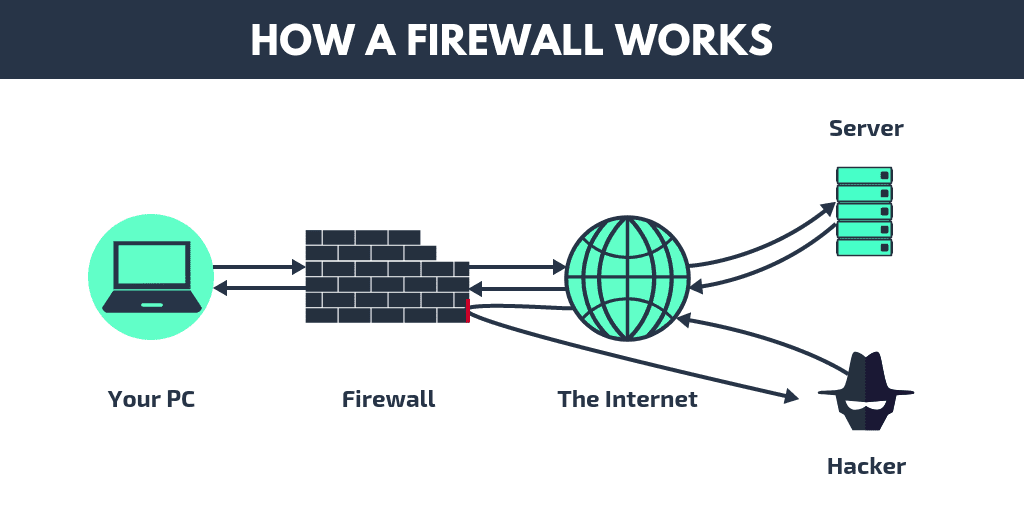
You can either get out of it or not. In general, firewalls are configured to allow packets that comply with ACL standards to enter the communication network.
In addition, firewalls play a key role in recording sensitive organizational information and assist Security experts in analyzing data. By reviewing firewall logs, network administrators ensure that internal or external users do not engage in suspicious activity.
Firewalls record the packet’s description, source and destination addresses, status, and conversion rate.
However, firewalls only show packet headers on the screen. Now that you have a brief overview of firewalls, it’s time to talk about different types of firewalls.
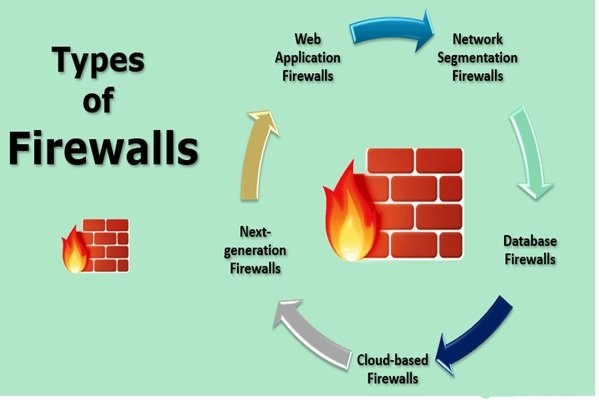
Types of firewalls
Firewalls are classified into different types, each of which is used based on the level of safety and capability they provide to organizations. Today, various firewalls are used in the world of technology, some of which are as follows:
Firewall Filtering Packet
It is a type of firewall typically placed on switches that act as an interface or connector to the web. The firewall separating the software package is created only on the OSI model of the enterprise layer. Filter firewalls are dependent on policies and standards defined by access control lists.
Packet screening firewalls gain access to the checklist by thoroughly examining the layout of the received packages to confirm that they are correct and aligned with the checklist. If the software package is inconsistent with the access control list policies, the package is discarded, and a report is prepared so that experts can review these reports in the future.
Surface gate firewalls
Surface circuit firewalls are another type of firewall. The circuit surface firewall works in the session layer in the OSI model, which is an intermediate layer between the application layer and the transport layer in the TCP / IP model.
This firewall monitors the connection process and the initial packets or packets in the TCP model to determine if a session request is valid.
The circuit-level firewall hides the details of the protected network from external traffic, which prevents abusers from accessing it. One advantage of circuit-level firewalls is that they are relatively inexpensive and keep private network information private, but these types of firewalls cannot scan and filter packets inside.
The following operations are used in this firewall:
- Each meeting is given a unique number.
- The information sequence is examined.
- Addresses, both origin and destination, are examined.
- The port number is recorded and stored.
This method is faster because it does less research on the content of the data, but because the content of the packets is not monitored, it has a more limited capability.
Firewall Inspector of the State House
Inspection firewalls, also called dynamic screening firewalls, have a mode that uses a table to communicate. The function of these firewalls is to compare the header of the new package with the information in this table and decide whether to communicate based on the protocol and status.
These decisions are based on the policies listed in the firewall and the related table. Modeled firewalls monitor all activities from when the connection is opened to when it is closed. The routing data packets used in the network are stored in the firewall table.
This mechanism does not forget the closed path sequence in the network, and data inspection is performed based on this information. However, these firewalls are vulnerable to denial-of-service attacks due to their complexity.
Non-load-bearing firewalls (proxies)
Proxy firewalls are barriers between systems/networks and the Internet, receiving user requests. Instead of establishing a direct connection to the Internet, proxy firewalls receive and send user dialogues and verify the response received from the service provider. They ensure that the data is provided to the user.
An essential advantage of these firewalls is that if a user on the network requests the data, they respond to the user with the ability to retain the previous requests from the data stored in their memory instead of returning to the server.
The above approach increases the network’s speed and responsiveness. These firewalls work in the OSI model’s application layer, or layer seven, and separate the enterprise network from the external one.
Firewalls of the next generation
Next-generation firewalls are a combination of packaged, state-of-the-art firewalls that block advanced and new-generation malware attacks and attacks targeting layer seven.
Virtual firewall
Virtual firewalls are gaining popularity. They are mainly used in cloud-based networks and architectures related to VMware ESXi, Microsoft Hyper-V, and public clouds provided by Microsoft, Google, and Amazon.
These firewalls monitor and secure the traffic of virtual and physical networks. Virtual firewalls are an essential component of software-driven networks.
Firewall software
Firewalls are software that all users have through the Windows operating system. They are software installed on the operating system that controls the entry and exit of traffic to the network or the operating system.
Home users and small and medium businesses mainly use this firewall model. Software firewalls protect systems against unauthorized access that threatens systems from the Internet. Potential benefits of these firewalls include sharing resources such as printers and scanners, changing Security policies, and adjusting configurations as a multilayer firewall with modes.
This firewall combines the firewalls we discussed. Multilayered advanced firewalls have complex functions. Multilayer inspection firewalls can build channels based on access control. Multilayer filter packets into the grid layer to ensure a valid session. In addition, the content of the packages is evaluated at the application layer.
Hardware firewall
Hardware firewalls are marketed as physical products that can be installed as hardware in the communication infrastructure.
Traditionally, firewalls installed inside routers allow the router to be used as a hardware firewall in a network. Based on the initial settings, hardware firewalls can prevent traffic and unwanted data from entering the network by default and create a secure data exchange stream.
This firewall model works in the form of closed filtering. It examines the headers related to the packages’ origin and destination. If the packages contradict the firewall policies, they are prevented from entering the network and discarded.
FAQ
What is a firewall?
A firewall is a security system that monitors and controls incoming and outgoing network traffic.
What are the main types of firewalls?
Common types include hardware firewalls, software firewalls, and next-generation firewalls.
Why are firewalls important?
They help prevent unauthorized access, protect data, and reduce security risks on networks and devices.