End-To-End Encryption; A Way To Secure Communication, What Is End-To-End Encryption And Why Do We Need It?
One of the safest methods of encryption today is end-to-end encryption. But what is this method of cryptography?
How does it work? In what cases is global cryptography limited?
Despite WhatsApp’s recent decisions about its security issues and changes to the messenger’s privacy policies (which were delayed due to user migration), the term end-to-end encryption is more common than ever. Is taken into consideration. But what does universal cryptography mean?
What is end-to-end cryptography?
The main purpose of this type of encryption is to ensure that the data sent by users is completely secure until they reach their destination and is sent encrypted.
In other words, in this method of encryption, there are only two parties to the communication who have access to plain text (which is professionally referred to as Plain Text).
Even so, owning one is still beyond the reach of the average person.
This will make users more confident because users are currently worried about the app developer selling their information to various companies, including advertising companies.
End-to-end encryption, however, fixes this problem. In other words, in this type of encryption, even the application developer can not see the message of the users.
Although end-to-end encryption is not specific to messaging and can even be used in email, etc., the reality is that in messaging, two-way encryption is far more important.
Other applications of this type of global encryption include password management tools that encrypt information end-to-end so that even the password management tool developer can not access the user’s passwords…
Of course, in the case of password management tools, the story is a little different, because in this case we are not related, and you are the only one who can view the data simply and plainly.
There are currently many media outlets that use such encryption methods. Among the media messages equipped with end-to-end encryption, we can mention WhatsApp, Telegram, Signal, etc.
In what cases is universal cryptography incapable?
Despite the security that end-to-end encryption provides, this method has its limitations. In fact, although encryption hides all of the user’s submitted content, and even the server will not have access to the user’s message, the server certainly knows what day and time you exchanged the message.
In some cases, this can provide hackers with specific information.
Another problem is that if someone can access your device, they can access your incoming and outgoing messages without any restrictions.
Therefore, having end-to-end encryption alone is not enough, and you still need a password to access the device (for example, a PIN code or biometric authentication).
This way, even if the device is stolen or can be accessed in any way, the security of the messages will not be compromised.
This problem will also exist on the other side of our relationship. In other words, if we physically secure the device ourselves, the other party may still not pay attention to this issue and cause the messages transmitted by us to be exposed.
Despite all the problems that exist, two-way encryption is now the safest way to transmit data, which is why most services, especially the media, resort to end-to-end encryption.
What is End-to-End or E2EE Encryption?
End-to-End Encryption is a model of encrypted communication in which only the parties to the communication can read the messages. In this method, messages are encrypted from source to destination.
No eavesdropper can access the keys needed to decrypt messages, even the Internet provider and the company that provided the communication software.
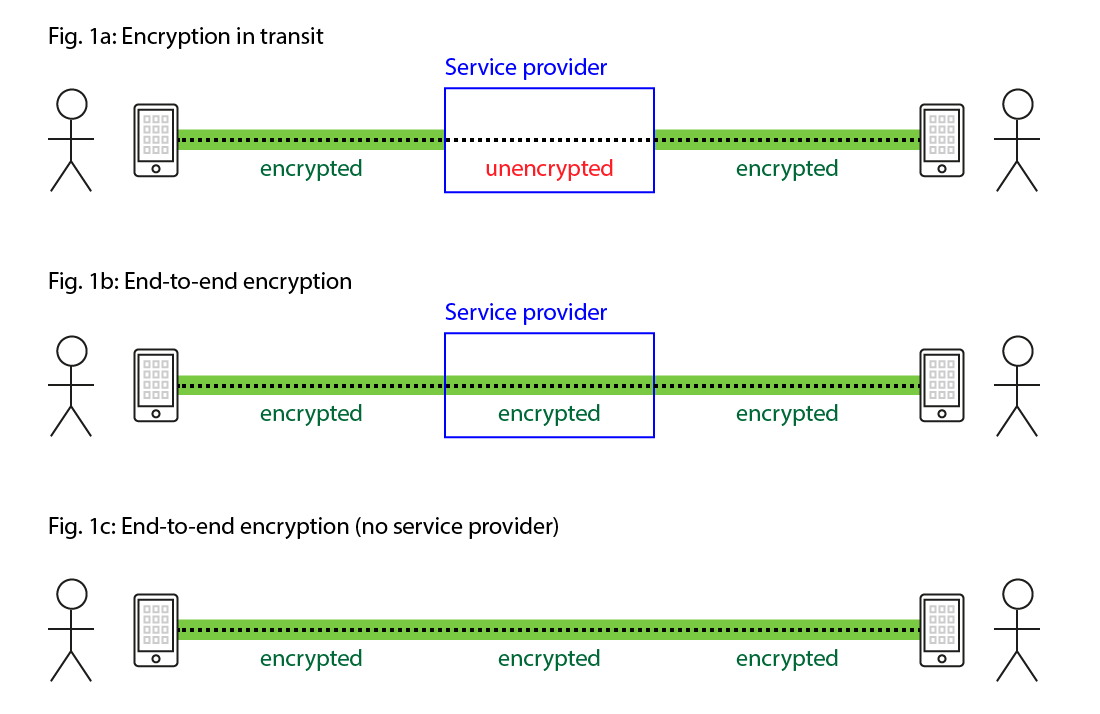
In the image below, Figures 2 and 3, the end-to-end encryption method is used.
You can see that communication is established along the way to the encrypted form. But in Figure 1, the information is readable for the provider company.
The encryption key used to encrypt and decrypt the message is stored only at the last point of communication, the device of the parties to the communication.
There are two potential vulnerabilities in the use of end-to-end cryptography. One is that each party must have the other party’s public key, and if the saboteur has access to one of the parties’ devices, they can use their own public key to carry out the man-in-the-middle attack. Give.
Also, if one of the communications devices falls into the hands of the saboteurs, for example, their conversations can be read to the saboteurs before and after encryption.
These vulnerabilities have nothing to do with end-to-end encryption and key exchange, and you need to secure your device.
The first communication software to make extensive use of end-to-end encryption was PGP, which encrypted email and its attachments.
Most instant messaging software, such as Telegram, Signal, and most recently WhatsApp, now use end-to-end encryption.
What is end-to-end encryption and why do we need it?
What is end-to-end
Depending on how trustworthy their owners are, this can be trivial or, conversely, very dangerous.
Global encryption benefits
Weaknesses of global encryption
The server could not read the messages, But he is certainly aware that the message was exchanged on a specific day and at a specific time. In some cases, just communicating with specific people may sharpen the tentacles.
Second, if someone has access to the device they are using for communication, they will be able to read all your messages and send messages on your behalf.