What Security Points Should Programmers Pay Attention To When Designing Software?
Applications, Systems, And Networks, Are Exposed To A Variety Of Cyber-Attacks, Such As Password Hacking, Dictionary Attacks, And Pervasive Search.
In the past, companies did not expect programmers to have a thorough knowledge of security issues, as this was the responsibility of security experts. Still, today one of the most critical tasks of programmers is to clean code free from common mistakes. In general, applications face two major security issues.
The first problem is the hidden vulnerabilities in the frameworks, libraries, or tools that programmers use to develop software. The second problem is poor coding, which makes software vulnerable to cyber-attacks.
These are just some of the goal-setting shareware that you can use. Today, most attacks that target enterprise infrastructure and networks are implemented through hidden vulnerabilities in applications running on client or server systems.
Therefore, as a programmer, it is essential to have complete information about attack vectors so that you do not inadvertently create access for hackers when coding programs.
Applications and their challenges
Daily applications are exposed to many types of cyber attacks. Hackers, like regular users, install and run the software, check its performance, and then search for vulnerabilities in the software. Since professional hackers are experts in the field of programming, they have a thorough knowledge of programming concepts and how to exploit vulnerabilities.
Directory navigation
Web-based application developers and web admins are always concerned about attacking Directory Traversal. In this attack, hackers evaluate the file system of the web server so that they can inject malicious commands into HTTP messages. In this technique, the hacker tries to test. In a web address, enter the server’s web directory structure several times.
After entering the directory, it goes back several times to reach the operating system directory and execute the active system level commands. To counter directory crawling attacks, you need to ensure that the systems are up to date with security patches and look for a blocklist of familiar characters in URLs like
Injection attacks
The biggest problem that applications face is injection attacks. Injection attacks occur for a variety of reasons. For example, may do it to extract information. Here, application software is used as an intermediary to attack a database. Hackers use this technique to insert various types of programming code instead of the data the software is waiting to receive. Injection attacks are divided into the following types.
SQL injection
Almost all database experts and web programmers are concerned about this attack. Programmers use structured Query Language (SQL) to implement dialogs on databases. Web and enterprise applications use structured query language to retrieve data from databases. For example, you might have an office-based software storing information in a database.
The program uses a query language to retrieve this data from databases and displays the information. In synthesized query injection attacks, the hacker uses the commands of this language to manipulate the data in the database. In this method, the hacker enters the standard code of the query language into the program and ensures that the program sends the above commands to the database.
The hacker enters SQL statements in a place that programmers or database administrators do not expect, such as username and password fields on the login page.
Figure 1 shows an example of an SQL code injection attack. In this figure, you will see a login page waiting to receive a username and password. When the user enters the information in these fields, this information is placed in SQL statements so the user can authenticate and log in. The command used for this purpose is the select command, which is used to find information in a database. When the user clicks the LOGON button, the choose command tries to find the username and password typed in the program.
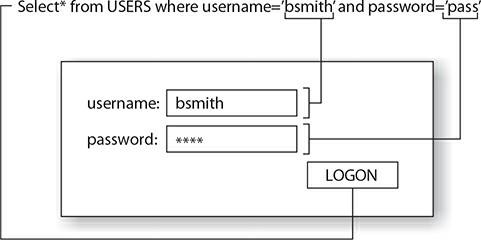
Figure 1
In the above example, the hacker has to ensure he gets the desired result after running a dialog because he does not know the valid username and password, so It tries to enter the SQL code as the password so that he may be able to log in. For example, one common technique used in this field is to insert database commands into the password box to execute an SQL code injection attack successfully:
pass’ or 1=1 —
The word pass is something that the hacker types as his password, which will not work because the hacker does not have an account in the application. The 1 = 1 statement is used as a condition in the select statement but is not tested as an actual password. The critical point is the” ‘” character used to close the particular command.
The “-” characters at the end of this command indicate a comment and are not usually a problem. However, there is a subtle point. In the main code, the programmer uses the” ‘” character in the actual select command, where this character specifies the end of that command. Now the two “-” feelings, which in the real world are only used by programmers to post comments, ignore the continuation of the original select command at the top line. Hence, in poor coding, this technique allows the hacker to log in.
Another major challenge that database programmers face is hackers’ changing the price of goods in an online store. The following command allows you to sign in, but it also executes an updated phrase that changes the price of all title table books to 50 cents:
pass’ or 1=1; update titles set price=.5 —
Another risk associated with applications is calling operating system commands or database servers to create user accounts. For example, the following command is an internal stored procedure in
Summons SQL Server allows the database developer to call an operating system command to gather information. In the example above, the hacker creates his account called SQL in Windows so that he can use it to log in to the target website. Fortunately, this technique cannot be used from SQL Server 2005 onwards because the procedure is stored
xp_cmdshell is disabled by default and should not be enabled for this reason.
pass’ ;exec master ..xp_cmdshell “net user from SQL password /add» –
The following command uses the same technique as before to add an account to the group of local system administrators. So that the hacker gets a back door with full management capabilities. This technique can also be used when xp_cmdshell is enabled, while on newer versions of SQL Server, it is disabled by default.
pass’ ;exec master ..xp_cmdshell “net localgroup administrators from SQL /add” –
How can we prevent the successful implementation of SQL injection attacks?
As mentioned, software security is one of the main tasks of programmers because security experts have limited maneuverability to deal with this attack model.
- Sanitization: Programmers must identify and clear any input from the user that can execute SQL code using patterns such as regular expressions. For example, they must remove a semicolon and two dashes from the information. Therefore, to protect data-driven applications, consider the following:
- Validation: Developers must verify the input and ensure that the number of characters that can import and the type of characters used is limited.
- Parameterized queries: Using parameter queries means that the input is not sent directly to a SQL statement but is sent as a parameter to the command, and only specific values are accepted. If the parameter value is correct, it is executed by SQL statements. The pattern of parametric dialogs is one of the most critical topics in the programming world that you should pay attention to.
Dynamic-Link Library Injection
- Dynamic Link Library (DLL) injection occurs when an application has to load a DLL into its address space and execute DLL code. The code in the DLL can be malicious code that the hacker wants to perform on the system. It is a complex and subtle attack vector; Therefore, if the programmer does not consider a dynamic library validation mechanism when building applications, it will be successfully implemented.
Inject lightweight directory access protocol
(Lightweight Directory Access Protocol Injection)
- Lightweight Directory Access Protocol Injection Attack occurs when a hacker fills out a web form in such a way that it usually uses form data to query the database by calling LDAP. In this case, the hacker enters the desired content and controls it, and the server runs them. Still, because the application developer did not approve any of the entries, the hacker Will be successful in executing commands.
Injectable markup language injection
(Extensible Markup Language Injection)
- Extendable Markup Language (XML) injection attack is similar to Square Code injection and LDAP injection, except that the hacker enters the XML code into the program. It is enough to validate the information to prevent the successful implementation of this model of attacks to solve this problem. If the application developer has not validated the input, the hacker can manipulate the application execution process by injecting XML data.
Buffer Overflow Attacks
Since most applications are written in the C and C ++ programming languages, hackers are still trying their luck at performing buffer overflow attacks. Buffer overflow is when a hacker sends a lot of information to the program and causes the data to overflow from the buffer. A buffer is an area of main memory used to store information sent to an application. Imagine a pillow like a glass of water with a specific capacity when it pours more than the capacity of the water into the glass. The buffer overflow attack does precisely the same thing. Figure 2 shows a simple example of a successful implementation of this attack.
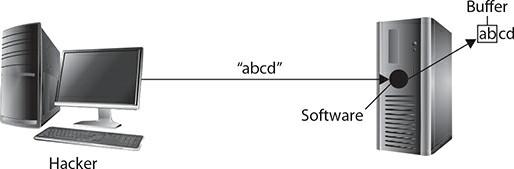
Figure 2
If the hacker can store information in memory outside the buffer zone, he can execute any code with administrative permission. The software exposed to this pattern of attacks is applications or services running in the operating system’s background.
Why are there vulnerabilities in applications?
You may ask why these attacks are successful. There are several reasons. Typically, hackers spend a lot of time working with technologies to discover their weaknesses and how to use them to carry out malicious activities.
In addition, programmers and software development teams intentionally place backdoors on their products so that they can make the necessary changes to applications in the future. Sometimes, hackers succeed in identifying and exploiting these backdoors. Developers are therefore forced to release patches to close these back doors.
The most important reasons for the success of attacks on applications are the following:
Improper Input Management: Input management and evaluation is another crucial task for software programmers and developers. Whenever data is sent to a program, the programmer must validate it and ensure it is appropriate.
In this case, an error is displayed to the user if the data is invalid instead of processing the information. If the programmer does not approve the input, hackers can inject malicious data into the program to control the software in a way that is not desirable.
Improper error management: Error management is another critical task of programmers. Programmers need to make sure that they correct any errors generated in the program and manage them properly so that the program does not run into serious problems. The improperly handled error can lead to program abuse. Additionally, it would help if you looked for error detection when software coding is complete.
Default configuration: When installing software or systems, change the default configuration as much as possible. It would help if you changed the defaults so that hackers have a lower chance of infiltrating programs. Hackers know the default settings of products and learn how to use the default settings to exploit systems.
Incorrect or poor configuration: Most hacking attacks are performed due to inaccurate or inadequate operating systems and application design. For essential software such as SQL Server, Exchange Server, and the like, you need to ensure you have the correct configuration.
Weak cipher: One of the biggest problems for applications is the lack of knowledge of programmers when using cryptographic algorithms. Unfortunately, some applications used by Windows and Android operating systems use weak encryption technologies or protocols. For example, some applications and firmware use the DES or 3DES symmetric algorithm to encrypt data. This encryption is inadequate and should be replaced by more powerful algorithms such as AES. Another example is the replacement of weaker encryption protocols such as TLS 1.0 and TLS 1.1 with the newer version of TLS 1.3.
Zero-Day Threats: One of the most common vulnerabilities that plague many companies is the zero-day threat, which refers to an unknown vulnerability that the seller is not yet aware of or has only recently become aware of. In Day Zero Vulnerability, there is not enough time to release the patch, and as a result, hackers can use it in a short time. The best way to deal with this attack is to employ intrusion detection and prevention systems.
last word
Security is one of the most overlooked aspects of application development that we use daily. Understanding how hackers infiltrate and damage a company’s infrastructure through applications running on systems is critical. A key point in discussing application software development is understanding that you can do your job as a programmer and perform security tests on the software you have designed after completing a software project with particular care and obsession.
In addition, a set of guidelines, checklists, and templates help you avoid common mistakes when coding. However, note that each programming language has its security patterns, which is not the case for all programming languages.
For example, Cisharp simplifies the coding process for programmers by introducing a concept called Garbage Collection. In contrast, languages like C do not have such a feature, and programmers must free up memory when allocating memory to dynamic objects.

