What Is SECaaS (Security as a Service)? A Clear Overview
With The Advent Of The Cloud, There Is Nothing About Your IT Infrastructure That Others Or Companies Can Do For You.
More And More Companies Are Turning To Cloud And Cloud Services Like Amazon AWS Daily To Provide The Computing And Storage Resources Needed To Run Websites And Applications.
SECaaS: Some companies rely on high-level programming interfaces related to online services to do their business. Others use hypervisors. Still, others use a complete platform, including the operating system, firmware, servers, and databases.
Others rely on software solutions and programs offered by third-party providers to do business. Such a super-service environment allows customers to meet their IT needs faster, easier, and more cost-effectively without implementing the infrastructure they need or worrying about developing, maintaining, and creating these resources.
Over time, almost everything that can be provided as a service, from backup to content delivery, sign-in, post-disaster recovery, and storage services, has taken over. Interestingly, security as a service is also a security cloud service provider.
What Is (SECaaS) Security As A Service?
Security as a Service (SECaaS) is an outsourced service in which a foreign company provides you with security capabilities and manages them. At its most basic, security as a service uses cloud security antivirus software to access the internet.
With the security approach as a service, security solutions are no longer provided locally. Traditionally, an organization’s IT department installs antivirus software, spam filter, anti-virus software, and other security tools on any device, network, or server at work and keeps the software up to date. However, the old way of doing this is costly.
Most companies spend a lot of money on hardware and licensing to use different software. Instead, security as a service allows security to access the same tools using only a web browser.
A single dashboard allows you to use a comprehensive mechanism for connecting to multiple network devices, resulting in considerable savings.
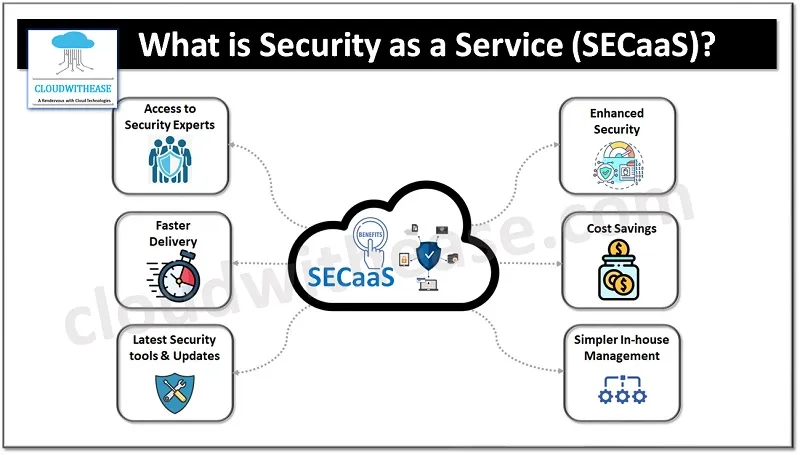
What are the benefits of security as a service?
The most significant security benefits as a service include the following:
- You work with the latest and most up-to-date security tools available. To be practical, antivirus tools must detect the latest viruses, threats, and even the latest unknown malware based on their pattern of behavior. When you decide to go for it cheaply and risk low bandwidth, you are only fooling yourself. In this case, you will no longer have to worry about employees’ antivirus updates and other programs because the antivirus will receive updates. feantiviruser, a vulnerability in the detected software is reported to network administrators, and security informs them.
- You hire security specialists. When you use the security approach as a service, you hire the IT security experts of the service provider company, who have better experience and skills than anyone on your IT team.
- Faster supply. The beauty of service delivery is manifested in giving your users instant access to security tools. Interestingly, SECaaS services are available on demand, so you can increase or decrease them to achieve the agility and speed you need.
- You need to focus on the organization’s most critical issues. Using a web-based interface or access to a centralized management dashboard can make it easier for the IT team to control internal security processes.
- It makes internal management easier. If you have protected data, it is not enough to keep it secure. You need to know how to react when a user accesses this data without a legitimate business reason to access it.
Cost savings. You do not need to buy hardware or pay for software licenses. Instead, you can focus your initial capital on operating costs that are variable and more than ever before.
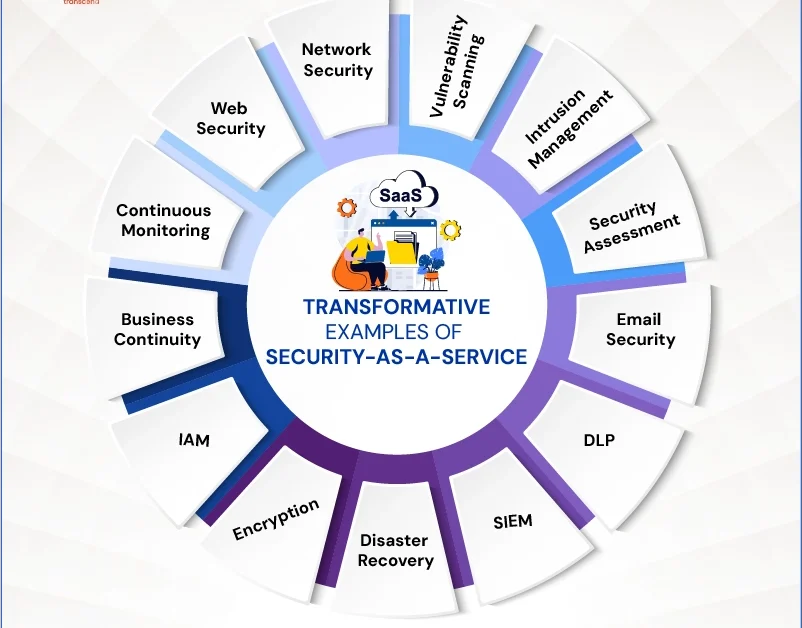
Examples of service-based security
Security as a service. Security software is provided on the organization’s cloud, enabling internal security management. Some of the solutions that are available and usable based on the above computing paradigm are as follows:
- Post-disaster recovery and business continuity. Tools to help you ensure your IT and operations return everything to its original state quickly.
- Continuous monitoring. Tools that allow you to manage risks by monitoring existing security processes continuously.
- Prevent the problem of data loss. Tools that secure all stored or in-use data.
- Email security. Protects your business from phishing, spam, and malicious attachments.
- Encryption. It makes your data unreadable and only allows private data to be decrypted with a private key.
- Identity and access management. Provides mechanisms for authentication, access to information, and validation of processes and users.
- Infiltration management: This involves detecting unusual events and behaviors using pattern recognition technology. These tools not only detect intrusions but also help manage them.
- Network Security. Tools and services that help you manage network access and distribute, protect, and monitor network services.
- Security assessment. They audit current security measures and examine whether the standard aligns with industry patterns.
- Security information and event management. It provides tools that aggregate information from reports and events and can be helpful during analysis to diagnose anomalies and potential intrusions.
- Scan vulnerabilities. Provide detection of any vulnerabilities in the network or IT infrastructure.
- Web security. Protects online applications that are publicly and promptly available to the public.
FAQ
What is SECaaS?
SECaaS (Security as a Service) is a cloud-based model where security services like antivirus, intrusion detection, and data protection are delivered over the internet instead of on-premises.
Why do businesses use Security as a Service?
Businesses use SECaaS because it reduces costs, provides scalable security solutions, and allows organizations to access advanced protection without managing complex hardware or software.
What are examples of SECaaS solutions?
Examples include cloud-based firewalls, identity and access management, email security, data loss prevention, and vulnerability management tools.