What is a Google dork?
In today’s world, Google is more than just a search engine that ordinary people don’t know about. Its many mysterious and practical features. One of the Google systems used to increase the security of websites is called Google Dork. This system is used as a reference for people who work in the field of cyber security. Just like other information sources, if honest people use the Dork system, it will have good consequences, such as increasing the security of the sites. But if the wrong people use this system, they can gain access to information they shouldn’t. Join us in the rest of this article to completely tell you what Dork is and its benefits.
Familiarity with the Google Dork system
Google Dork, also known as Google Hacking, has provided access to confidential information such as usernames and passwords for Internet users. In other words, this Google system allows users to access confidential information that is not easily found on websites.
The Google Dork system is a favorite of hackers who need information for cyber attacks. Note that it is impossible to hack different sites or software using this system directly. In general, this system provides information to users, which can lower the security of sites.
If you know a little bit about how Google works, you know that this search engine has robots called crawlers that index all the information on websites except for those specified in robots.txt. This feature allows everyone around the world to use the Google Hacking database.

Google Dork is not a specific website or an extension of the Google site; You can access this feature only by writing several operators. Each of these operators gives you specific tasks, such as searching only one site.
What are the benefits of Dork?
Dork is one of Google’s attractive but slightly dangerous features, which ordinary users can also use some of its operators to search better on the Internet. For example, if you want to access a PDF download link directly or download a movie with a specific extension, you can use dork operators. In other words, this feature is designed to make it easier for you to access Internet content.
One of the great advantages of the Google Dork system is that if you plan to check the security of your site, you can use this system to check all the ways to penetrate your site. Dork operators can also display information such as site logs. The interesting thing is that Google Dork is not a hard system that you can’t work with; Dork is just a string of phrases given at the beginning or end of the content.

Is Google Dork safe?
Using Google Dork is safe for all users; however, when using the Google Dork system, Google records all your identity information, so do not look for illegal content using this system. Also, if you bypass Google and change your IP, Google will still have access to your original IP.
How can we access content using Dork?
Using Google Dork can provide you with a wide variety of information, but how was this information obtained?! Google has crawlers that search the contents of websites all the time; these robots have access to all websites and index the information from these pages. These robots can index the information of all sites as soon as they become available. This issue has caused hackers to use Google Dork to use web content. This work, which can be used to increase security or hacking, is called Google Hacking.
What are some dork functional operators?
To use Google Dork, you must use its operators when searching in Google. Finding information about SEO backlinks can be mentioned among the types of things you can do with Google hacking operators. In this section of what Dork is, you will get to know some of the most popular Google Dork operators.
1. Cache operator
The cache operator is known as one of the most useful Dork operators. Using the Cache operator shows each website in cache format. Administrators use this operator when the uploaded content is not displayed in the search engine. For example, you can search for “cache:wikipedia.com.”
2. FileType operator
The filetype operator is one of the most widely used Google Dork operators, which you can search for specific file extensions on the Internet. This operator is one of those operators that can deepen your search on the Internet. For example, if you want to search among MP4 files, you can use “filetype: MP4” at the end of your search term. Another example of using File Type is when users look for a link to download a PDF file.
3. All intext operator
The All intext operator is used when you want to search all the words you want in the texts available on the Internet. For example, when looking for an article with words like Hack, Security, and Computer, you can use the phrase “allintext: hacking tools.”

4. Inurl operator
Users can use the Inurl operator to search among URLs with a specific word. For example, you can search for “inurl: google” among URLs that contain the word google.
5. Intitle operator
The Intitle operator, as its name suggests, is used to find specific words in the title of sites. For example, if you are looking for the word Friend among the titles of different sites, you can use the phrase “intitle: Friend.” This operator is mostly used when looking for a special word in the title of the sites.
6. Intext operator
The Intext operator is used when you want to return a string of specific characters in all texts. This operator works just like the All intext operator, but the only difference is that the Intext operator is used for a string of words. For example, you can use the intext: Fade” operator to search for the term “Fade.”
7. Inanchor operator
Anchor texts are found in promotional materials called reportage. If you are looking for a specific string of words in these ads, you should use the Inanchor operator. In some cases, you will need this operator when you are looking to buy or use the services of a site. For example, anchor: “Lifehack” is used to find anchor texts with the word life hack.
8. Arithmetic operators
There are some operators in the Google system; if you use them, you can get specific results. For example, among these operators, we can mention “+,” which searches for two separate words in Internet texts. In the following, we will learn more about these operators:
+ operator: You can use the + operator in cases where you are looking for several specific words in the content of the sites. You can use this operator like “Life + Hack.”- operator: If you are looking for a word on the web but don’t want to find a specific word in the displayed content, you can use the – operator.
Operator |: logical operator |, also seen in mathematics and programming language; it is used to search for one with both words. In other words, if you search for “Hack” | “Life,” Dork will show results that contain either one of the words or both words in the text.

How to deal with Google Dork?
Google Dork is one of the attractive features of Google for users, but if you are one of the website administrators and want to prevent your content from being shown in this feature, you can use the following measures.
1. Using the robots.txt file
Using the robots.txt file is one of the most common methods site administrators use to hide their site content from Google Dork. Using this file when you plan to make some of your content private is recommended to protect it from search engine bots.
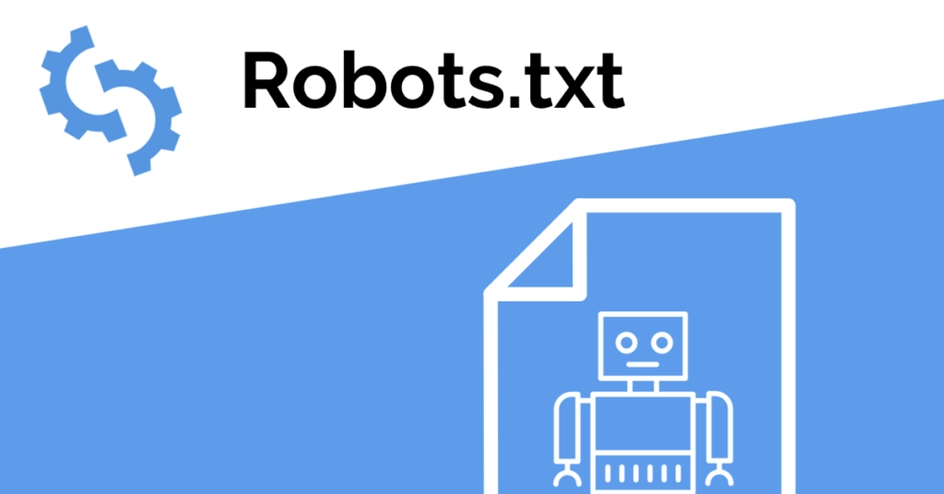
2. How to make a robots.txt file
To create robots.txt, you must go through the steps in this section. In general, there are four important commands in this file, which include: Disallow, User-agent, Allow, and Sitemap. The role of these commands is as follows:
- Allow: Use the Allow command for the sections you intend to allow access to
- Disallow: Use the Disallow command in sections where you intend to deny access to all robots
- User-agent: Use the User-agent command to command the desired bots
- Sitemap: If you want to show the sitemap to search engine bots, use the Sitemap command
If you intend to use the mentioned commands, you can command all robots with *. For example, if you intend to use the User-Agent command, you can give a command to all bots by adding * to the end of this statement, such as “User-agent:*.” However, for example, you can specify commands for Google bots by adding the phrase GoogleBot instead of the * at the end of the phrase.
3. Using the Disallow command
Using the Disallow command is allowed when you do not intend to provide a group of content on your site, such as videos, to robots. For example, if you want to prevent the robots from sharing the photos you put on your site, you should enter the following commands in robots.txt:
User-agent:*
Disallow: /photos
In the commands above, the user-agent command is accompanied by an asterisk indicating that all bots must follow the command. In the second line, the Disallow command instructs all robots not to access the photos folder. It is interesting to know that access to robots.txt commands is easily possible on all sites. You can see the commands of each site by adding robots.txt/ at the end of the URL of each site.
4. Request removal from the search engine
If the contents of your site are inadvertently made available to users by search engine robots, you can request the support of these sites, such as Google, to block the access of the robots to keep your contents hidden. Another way to keep your information safe on your website is to use usernames and passwords for files.

How to find log files using Dork
Log files contain confidential information, such as users’ passwords, which exist on all sites. Of course, normally, all confidential information is removed from these files, including reports, errors, and accesses. Access to these logs can lead hackers to important information. If the logs become available to hackers, they can access information such as the following:
- User login and logout information
- Content Management System version
- Directory information of files
- Services version
- Errors
To find the information in the log files, hackers can access the usernames in the log files by combining the terms username and log.
Accesses you can have using Dork.
After we understand how to find the log using Dork, we can access various things on the Internet, such as FTP servers. Search engines like Google also access FTP websites in addition to HTTP. These servers can also be accessed using Google’s Dork feature. In the following, we will get acquainted with examples of using the Google Dork system.

1. Access to ENV files
Files with the .env extension are files used by web development frameworks. These frameworks use .env files to announce changes to their configuration online and offline. Env files should not be placed in folders that are easily accessible to the public. If this file is available to the public, hackers can manipulate your site’s changes and disable your site. Even though Dork can access .env files, some web developers still ignore this issue.
2. Access to the email list of users
One of Dork’s strange accesses, which has turned this system into a hacking tool, is access to the user list. You can access users’ emails using the .xls extension among the files available on the Internet. Google Dork’s complex capabilities are achieved by combining two or more operators. Some other accesses of Google Dork are as follows:
- Access to live CCTV cameras
- Access to all types of files, such as music and PDF
- Access to expert weather information
- Access to Zoom video rooms
- Access to SQL Server dumps
- Access to the admin page of WordPress platforms
- Access to government documents
- Access sites to change the cPanel password
Google Dork courses are prerequisites for entering the cybersecurity job market.
Today, search engines, especially Google, have many uses that can no longer be considered normal search engines. Aside from their weird access to our daily lives, features like Google Dork allow access to all web content as a single source. Note that Google Dork is not a particular site or plugin but a function in the Google format.
Google Dork is not only for special users such as security professionals, but ordinary users can also use it. For example, if you can use the FileType operator, you can have better access to your favorite content on the Internet. Of course, if you are one of the site administrators, you can prevent search engines from accessing your content by taking some actions, such as creating a robots.txt file.