Different Types Of Cyber Security Threats – What Is Cyber Security?
Cyber Security Is The Protection Of Internet-Connected Systems Such As Hardware, Software, And Data Against Cyber Threats.
Individuals and companies do it to protect sensitive data from unauthorized access to data centers and other computer systems.
A robust cyber security strategy can provide a good defense against malicious attacks. Attacks aimed at accessing, altering, deleting, destroying, or extorting that may render organizational data unusable or deleted. In addition, cyber security is very useful in preventing attacks that aim to disable or disrupt the performance of a system or device.
Why is cyber security essential?
With the increasing number of enterprise users, devices, and applications and the rising flood of data, most sensitive or confidential, cyber security has received particular attention. Cybersecurity has been called one of the most popular trends in the world of information technology since 2023.
The increasing volume of attacks and sophisticated techniques used by cyber attackers to attack infrastructure have made detection more difficult. So sometimes, security experts cannot identify these attacks without using specialized tools.
What are the components of cyber security, and how do they work?
Cyber security can be divided into several parts whose coordination plays a vital role in protecting the organizational infrastructure and adopting security strategies. These sections are as follows:
- Application security
- Information or data security
- Network Security
- Disaster recovery/business continuity planning
- Operation security
- Cloud Security
- Critical infrastructure security
- Physical security
- End-user training
Maintaining cyber security has caused organizations to face a severe challenge due to the complexity of the techniques used by organizations to attack the infrastructure. Traditional approaches to respond to these attacks, where resources were placed in isolated networks, can only be used in certain situations. Sometimes organizations have to connect the leading grid to the Internet.
The same issue makes corporate networks defenseless against lesser-known threats. To solve this problem, security experts have to use more active approaches that are more compatible with the developments in the world of cyber security.
Today, various organizations are in the role of cyber security consulting the help companies in this field. For example, the National Institute of Standards and Technology (NIST) recommends that you adopt continuous monitoring and real-time assessments as part of a risk assessment framework to defend against known and unknown threats.
Now, we come to the critical question, what are the benefits of implementing and maintaining cybersecurity practices for organizations? Among these achievements, the following should be mentioned:
- Business protection against cyber-attacks and data breaches.
- Data and network protection.
- Prevent unauthorized access of users to resources.
- Improved crash recovery time.
- Security of end users and endpoint devices.
- Compliance with legal regulations.
- Business continuity.
- Increasing trust in the company among developers, partners, customers, shareholders, and employees.
What are the different types of cyber security threats?
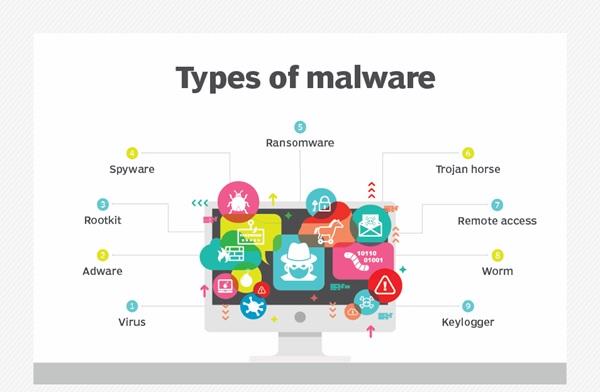
The process of keeping up with new technologies has made security policies face new threats and challenges. To protect information and other assets from cyber threats that take different forms, it is essential to have basic knowledge about cyber threats. Among these threats, the following should be mentioned:
-
Malware is malicious software in which any file or program is used to harm the computer user. This includes worms, viruses, trojans, and spyware.
-
Ransomware is another malware. This malicious file contains malicious code that locks the victim’s system files. This process is done through encryption, and the hacker asks the victim to pay a ransom to regain access to the files.
-
Social engineering: An attack that relies on human interaction. The episode is designed to trick users into inadvertently breaking security procedures to expose sensitive, protected information.
-
Phishing: A form of social engineering in which fake emails or text messages are sent that look like emails from legitimate or known sources. Phishing attacks, some of which are accidental, are used to steal sensitive data such as credit card or login information.
-
Targeted phishing (Spear phishing): A phishing attack targeting specific users, organizations, or businesses.
-
Internal threats: refers to security breaches or damages caused by malicious activities of employees, customers, or contractors. Insider threats can be harmful or negligent.
-
Distributed Denial of Service (DDoS) attacks in which multiple systems send the same traffic to a target, such as a server, website, or another network resource, to disrupt their performance. When these attacks become too numerous, the equipment cannot respond to legitimate requests.
-
Advanced persistent threats (APT)are long-term targeted attacks in which an attacker infiltrates a network and hides his identity for an extended time to steal data.
-
Man-in-the-Middle attacks are eavesdropping attacks that include the attacker’s interception and transmission of messages from both sides. These attacks are carried out in such a way that the identity of the hacker remains anonymous.
-
Other common attacks in this field include botnets, drive-by-download attacks, exploitation kits, malicious advertisements, vishing, cross-site scripting (XSS) attacks, SQL injection attacks, and compromising commercial emails. BEC) and misuse of Zero Day.
What are the most critical challenges of cyber security?
Hackers constantly challenge cybersecurity with data deletion, privacy breaches, security plan disruption, and cyber security strategy changes. The number of cyber attacks is not expected to decrease shortly. Additionally, increasing entry points for attacks, such as the introduction of the Internet of Things (IoT) into the IT world, increases the need to secure networks and devices.
One of the most problematic elements of cyber security is the evolving nature of security risks. Hackers find new ways to attack infrastructure as new technologies emerge and are used differently. This issue has made it difficult for cyber security experts to adapt to these changes and update security methods to deal with threats. Ensuring that all elements of cyber security are constantly updated to protect infrastructure from vulnerabilities is just one of the problems facing security experts. This is primarily a big challenge for small organizations that don’t have enough IT staff.
Organizations can potentially collect a lot of data about people using one or more services.
Prevent cloud penetration. As more data is collected, the likelihood of a cyber attack to steal personally identifiable information (PII) doubles. For example, an organization that stores PII in the cloud may be vulnerable to a ransomware attack. For this reason, organizations should do everything they can to protect their infrastructure from cloud attacks.
Cybersecurity programs must also address end-user education, as employees may accidentally bring viruses into the workplace on their laptops or mobile devices. Regular training increases employees’ awareness of security problems and cyber attacks, which is essential in dealing with cyber threats.
Another challenge facing cybersecurity is the lack of qualified cybersecurity personnel. As the volume of data collected and used by businesses increases, the need for cybersecurity staff to analyze, manage and respond to incidents increases. The ISC2 Institute estimates that the gap between vacant security positions and qualified employees will reach 3.1 million open jobs in the next few years.
How is automation used in cyber security?
Automation has become an integral component of protecting companies against the increasing number and complexity of cyber threats. The use of artificial intelligence (AI) and machine learning in departments that interact with large volumes of data can help improve cybersecurity in three main categories:
- Threat detection: AI platforms can analyze data, identify known threats, and predict new threats.
- Threat response: AI platforms also build and automatically enforce security protections.
- Increased time for security professionals: Security professionals often face repetitive tasks and alerts. Artificial intelligence can prevent employees from getting tired of repetitive and tedious tasks by accepting part of this work and providing automation mechanisms for extensive data analysis.
- Other benefits of automation in cyber security include attack classification, malware classification, traffic analysis, adaptive analysis, and more.
Cybersecurity solutions available
Cybersecurity vendors usually offer different security products and services. Standard security tools and systems are as follows:
- Identity and Access Management (IAM)
- Firewalls
- Endpoint protection
- Anti-malware
- Intrusion Prevention/Detection Systems (IPS/IDS)
- Data Loss Prevention (DLP)
- Endpoint detection and response
- Security Information and Event Management (SIEM)
- Encryption tools
- Vulnerability scanners
- Virtual private networks
- Cloud Workload Protection Platform (CWPP)
- Cloud Access Security Broker (CASB)
- Familiarity with job opportunities in cybersecurity
As the cyber threat landscape continues to grow and new threats emerge, such as IoT threats, individuals with cybersecurity awareness and hardware and software skills are needed.
- Chief information security officer: is a person who implements the security program throughout the organization and supervises the operations of the information technology security department.
- Security specialist (Chief security officer): an executive responsible for a company’s physical and cyber security.
- Security engineers: protect company assets against threats, focusing on controlling the performance of IT infrastructure.
- Security architects are responsible for planning, analyzing, designing, testing, maintaining, and supporting an organization’s critical infrastructure.
- Security analysts have multiple responsibilities, including planning security measures and controls, protecting digital files, and conducting internal and external security audits.
- Penetration testers: Ethical hackers who test the security of systems, networks, and applications and look for vulnerabilities that malicious agents can exploit.
- Threat hunters: Threat analysts aim to discover vulnerabilities and attacks and mitigate them before they endanger businesses.